INTRODUCTION:
A virtual LAN (vLAN) is any broadcast domain that is partitioned and isolated in a computer network at the data link layer (OSI layer 2) (wikipedia)
vLANs works by applying tags to network frames and handling these tags in networking systems.
——
I love how USG has faced up the vLAN challenge.
Their starting point is working with vLAN as if it were a layer 3 object and not layer 2 of the OSI model.
The idea behind USG is thinking vLAN is a new LAN with a different IP Address”. Are you a little bit confused? Yes? I also was at the beginning but now I’m enthusiastic of this new approach.
Let’s explain better with an example directly from my Lab Network.
In my Environment I needed to create 2 vLAN. The first one to address the iSCSI protocol and the second to manage the Backup traffic.
I chose #40 to point up iSCSI vLAN and #50 the Backup.
I went directly to USG user interface and created the vLANs from Network menu as shown in figure 1, 2 and 3
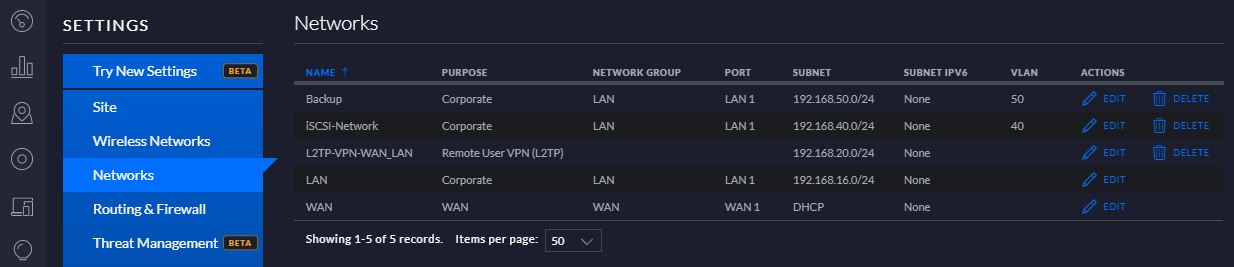
Figure 1
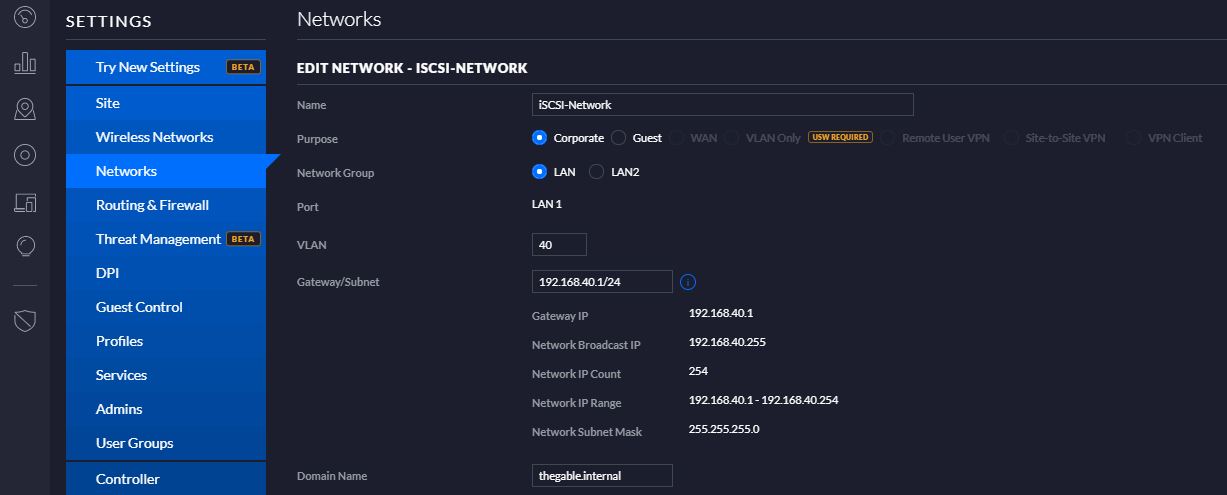
Figure 2
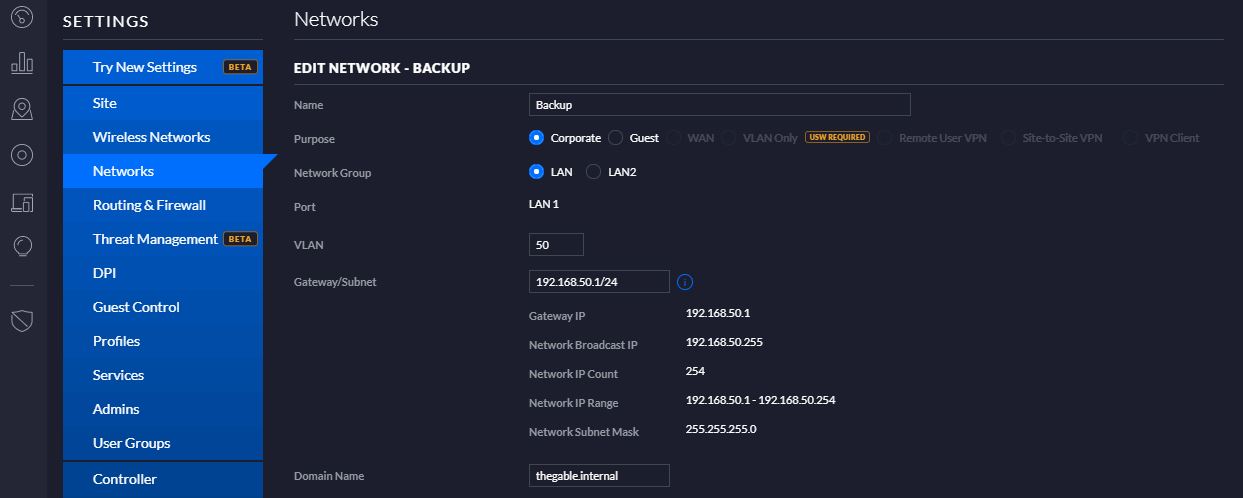
Figure 3
The next step is enabling routing between the new networks and the original LAN.
The task is performing selecting Switch ports from Profiles Menu.
As shown on figure 4 I set up an easy rule to let the networks talk to “each other”. In this case LAN to iSCSI as Figure 4
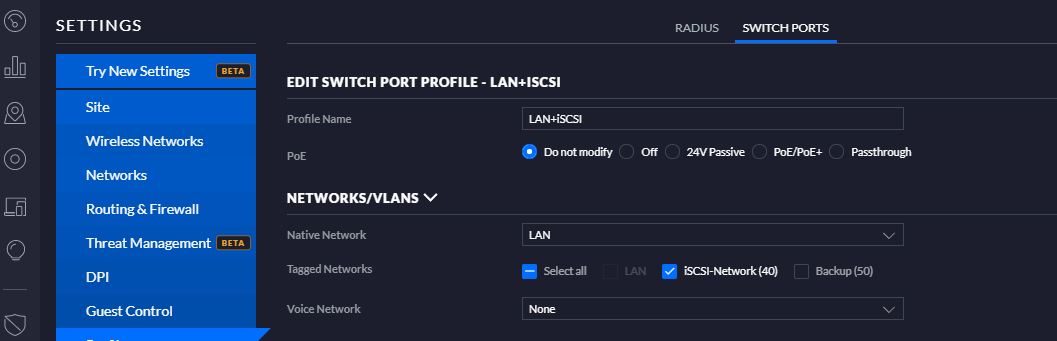
Figure 4
Now the last step. Enabling traffic from and to the Networks. In a simple word I worked at Firewall level.
I spent some hours to understand the options the USG can offer to their customers because it’s possible to set up many rules to manage traffic among LAN (LAN-IN and OUT), WAN (WAN-IN and OUT), GUEST (IN and OUT) and LOCAL (WAN/LAN/GUEST)
Really many many options but with a little patience, you can tune your networks answering to any security design.
In this example, I just created rules to manage the traffic LAN IN (FIGURE 5 and 6)
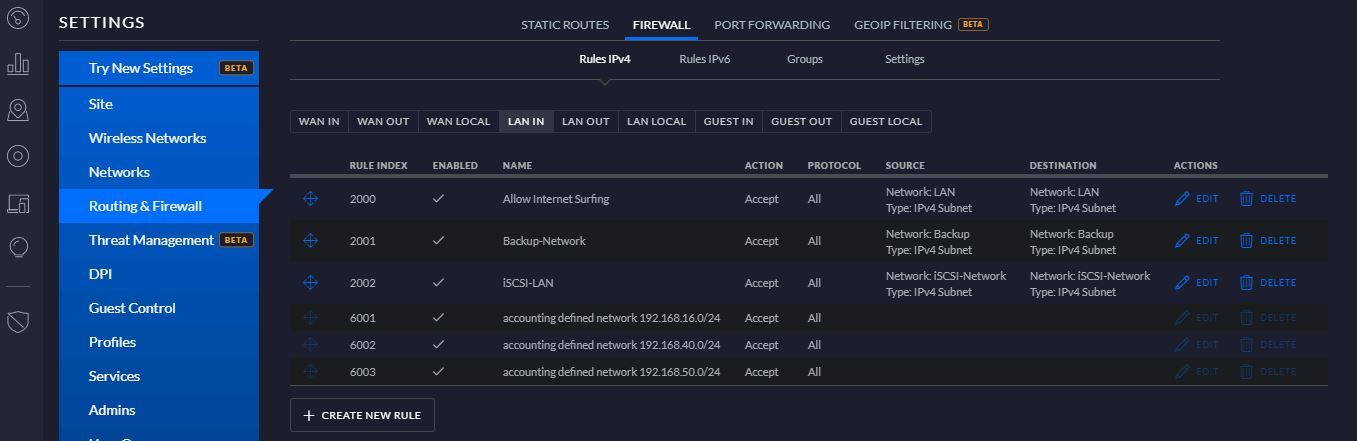
FIGURE 5
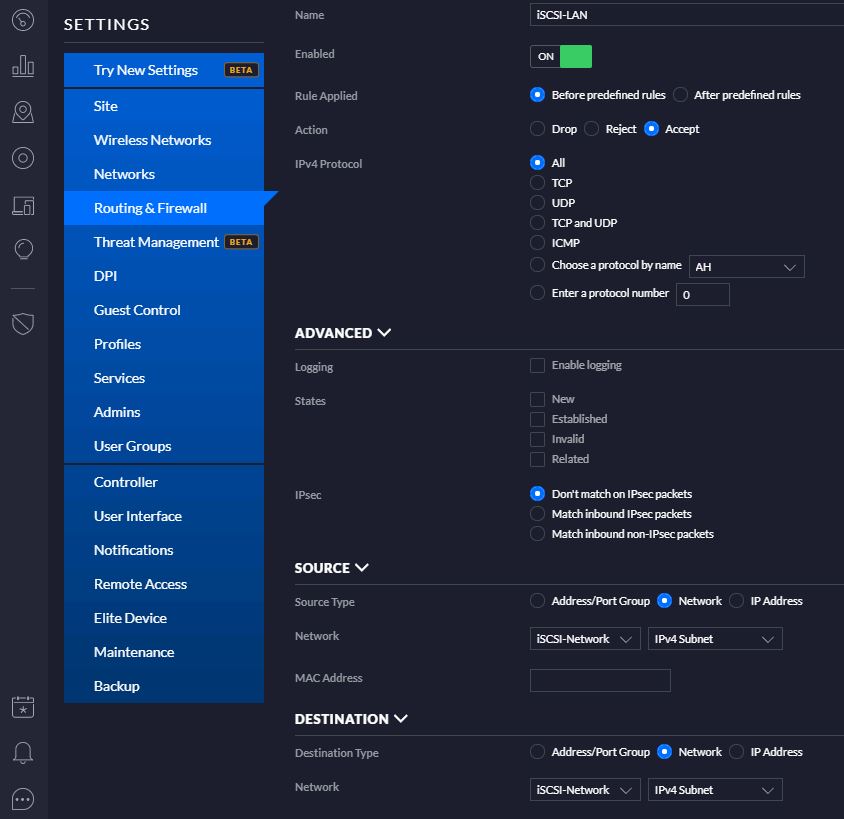
FIGURE 6
Before ending this article two more notes:
If you want to grant the Servers connected to LAN to surf on Internet, you just need to set up a LAN-IN and a LAN-OUT rule.
To work with vLAN you need to buy an Ethernet Switch vLAN compliant
